Most security teams are not suffering from a lack of visibility. They are suffering from an inability to keep up.
Modern organizations deploy dozens of vulnerability scanning tools across infrastructure, applications, containers, and cloud platforms. Every one of those tools produces findings. Every finding becomes a ticket. Every ticket requires analysis, prioritization, and coordination with engineering teams that already have competing priorities.
The result is predictable: vulnerability backlogs that grow faster than they shrink.
Security teams now discover vulnerabilities far faster than they can remediate them. Meanwhile, attackers exploit newly disclosed vulnerabilities within days. The gap between detection and resolution continues to widen.
Visibility alone does not improve security posture. Dashboards do not reduce attack surface. Lists of vulnerabilities do not remove risk.
Unified vulnerability management is emerging as the operational model that closes this gap. Instead of forcing teams to manage fragmented findings across tools and workflows, it consolidates vulnerability intelligence and helps organizations move from detection to actual resolution.
What Is Unified Vulnerability Management?
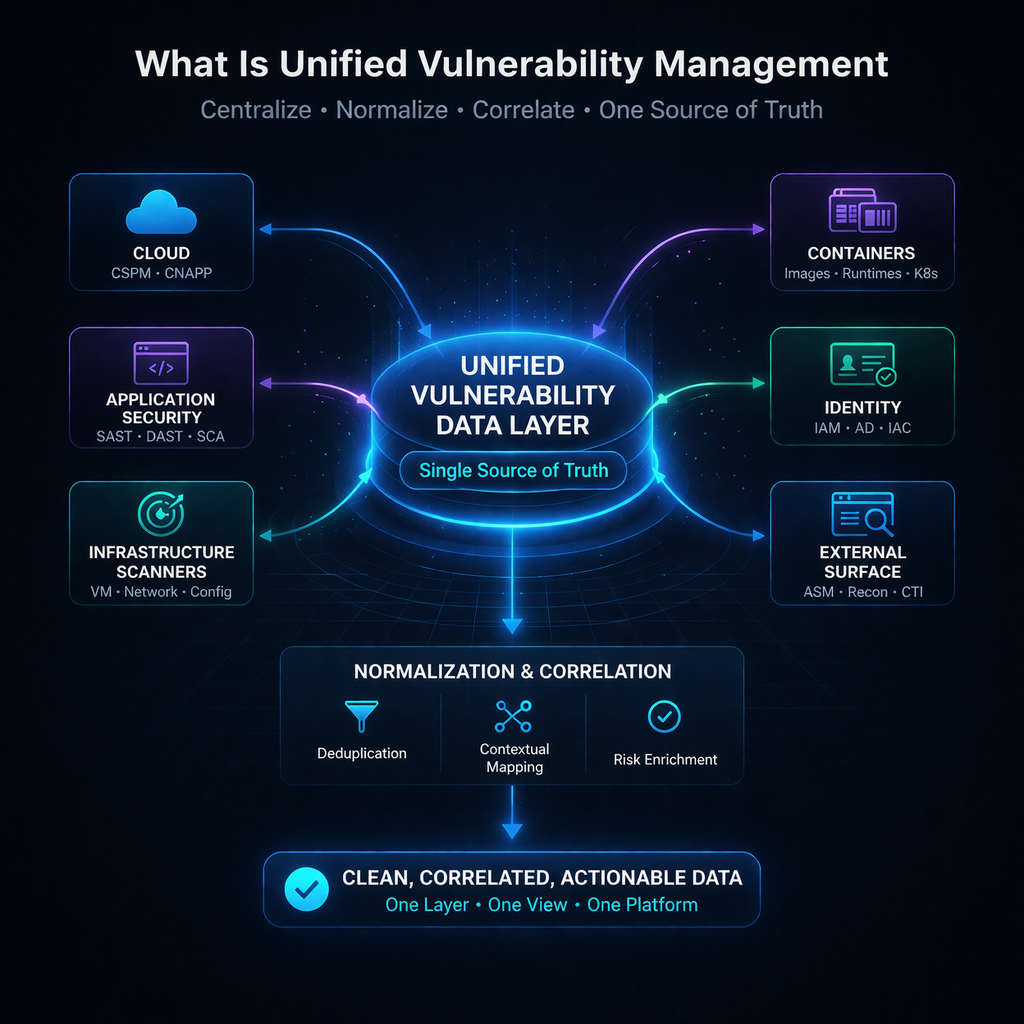
Unified vulnerability management (UVM) is a cybersecurity approach that consolidates vulnerability detection, prioritization, and remediation across cloud infrastructure, applications, and systems into a single platform. Instead of managing findings across multiple tools, UVM provides a unified view of vulnerabilities and helps organizations resolve risks faster by prioritizing exploitable attack paths.
In most environments today, vulnerability data comes from many different sources:
- cloud security tools
- application security scanners
- infrastructure vulnerability scanners
- container and image scanners
- attack surface management platforms
Each tool identifies risks independently, producing overlapping alerts and fragmented data.
A unified vulnerability management platform aggregates these findings into a single operational layer. It normalizes vulnerability data, correlates risks across environments, and provides centralized vulnerability prioritization.
This approach improves security operations in three key ways:
Consolidation of vulnerability data
Instead of juggling multiple dashboards, teams work from a single source of truth.
Risk-based vulnerability management
Vulnerabilities are prioritized based on exploitability, asset exposure, and real attack paths rather than raw severity scores.
Faster vulnerability remediation
Unified workflows allow security and engineering teams to collaborate on resolving risks instead of simply tracking them.
The goal is not just visibility. The goal is measurable reduction of organizational risk.
Why Traditional Vulnerability Management Is No Longer Enough
Traditional vulnerability management was designed for a very different era of infrastructure.
Security programs once focused on relatively static environments: on-prem servers, predictable patch cycles, and a limited number of scanning tools. Today’s environments look nothing like that.
Organizations now operate across multi-cloud infrastructure, containerized workloads, and rapidly changing development pipelines. Each environment introduces new attack surfaces and new vulnerability data streams.
The traditional model begins to break down in several ways.
Siloed scanning tools
Most organizations rely on multiple vulnerability scanning tools to cover infrastructure, applications, and cloud environments. Each tool reports vulnerabilities independently, forcing security teams to manually correlate findings.
Fragmented vulnerability data
Because vulnerability data lives in separate platforms, teams lack a unified view of organizational risk. Duplicate findings, inconsistent severity scores, and disconnected asset inventories create confusion during triage.
Manual remediation workflows
Even after vulnerabilities are prioritized, remediation often requires manual coordination. Security teams open tickets, engineering teams investigate, and fixes may take weeks to implement.
Unmanageable vulnerability backlogs
The number of vulnerabilities discovered daily now exceeds what most teams can realistically resolve. New findings arrive faster than tickets can be closed.
This creates a fundamental problem.
Security teams often achieve excellent visibility. But visibility does not equal risk reduction.
Without an operational system to prioritize and resolve vulnerabilities quickly, organizations remain exposed despite knowing exactly where their weaknesses are.
The Vulnerability Remediation Gap
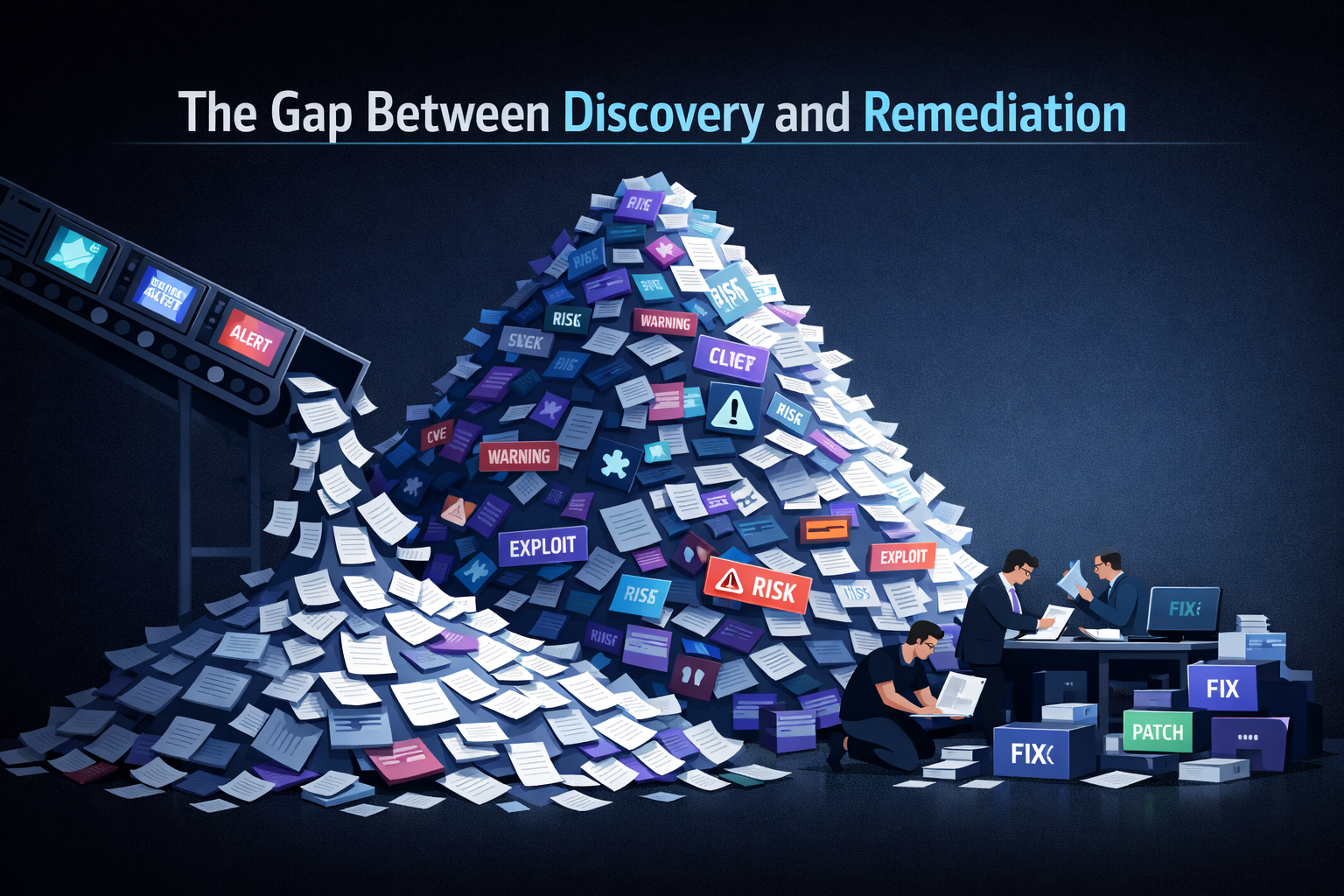
One of the most significant problems in modern cybersecurity is the gap between vulnerability discovery and remediation.
Security tools identify vulnerabilities quickly. Fixing them takes much longer.
Attackers frequently begin exploiting vulnerabilities within days of disclosure. In many organizations, remediation timelines stretch to several weeks or even months. During that window, exposed systems remain vulnerable.
Several operational factors contribute to this gap.
Growing vulnerability backlogs
Security teams may receive dozens or even hundreds of new vulnerability findings every day. Many organizations accumulate tens of thousands of unresolved vulnerabilities.
Limited human capacity
Each remediation ticket often requires coordination between security analysts, system owners, DevOps engineers, and infrastructure teams. The manual effort involved slows the entire vulnerability management lifecycle.
Cross-team coordination challenges
Security teams typically identify risks, but engineering teams own the systems that must be fixed. This creates friction, communication delays, and competing priorities.
The result is a familiar scenario: organizations know exactly where vulnerabilities exist, yet lack the operational capability to resolve them quickly.
Closing this remediation gap is the core objective of unified vulnerability management.
How Unified Vulnerability Management Works
Unified vulnerability management platforms create an operational pipeline that connects vulnerability detection directly to resolution.
Instead of treating scanning, prioritization, and remediation as separate processes, UVM integrates them into a continuous workflow.
Centralized Vulnerability Data
The first step in unified vulnerability management is consolidating vulnerability data from across the security stack.
Modern organizations run many different vulnerability scanning tools, including:
- cloud security platforms
- application security scanners
- infrastructure vulnerability scanners
- container security tools
Each tool reports findings using its own format, severity scoring system, and asset identifiers.
UVM platforms normalize this information into a unified data model. This creates a centralized repository of vulnerability intelligence across cloud environments, applications, and infrastructure.
The result is a single source of truth for vulnerability data, eliminating duplication and reducing analyst confusion.
Risk-Based Prioritization
Once vulnerability data is centralized, the next step is prioritization.
Traditional vulnerability management relies heavily on static severity metrics such as CVSS scores. While useful, these metrics often fail to reflect real-world risk.
Unified platforms enable risk based vulnerability management by incorporating additional context such as:
- exploit availability
- reachable attack paths
- asset criticality
- exposure to the internet
- real-world threat intelligence
By correlating this information, the system can identify which vulnerabilities are actually exploitable in a specific environment.
This dramatically improves vulnerability prioritization and helps teams focus their efforts on risks that matter most.
Automated Remediation and Mitigation
The final stage of unified vulnerability management is resolution.
Modern platforms accelerate vulnerability remediation through several mechanisms:
- automated remediation workflows
- built-in remediation guidance
- security-as-code fixes
- mitigation controls when patches are unavailable
In many cases, vulnerabilities cannot be immediately patched due to legacy software, vendor limitations, or operational constraints.
Unified platforms therefore provide mitigation strategies that reduce exposure until a permanent fix becomes available.
This combination of prioritization and remediation automation enables organizations to shrink vulnerability backlogs while reducing operational effort.
Unified Vulnerability Management vs Traditional Vulnerability Management

Key Benefits of Unified Vulnerability Management
Organizations that adopt unified vulnerability management typically see improvements across several operational dimensions.
Reduced Vulnerability Backlog
Unified visibility and intelligent prioritization help teams focus on the vulnerabilities that are actually exploitable.
Instead of chasing thousands of alerts, analysts concentrate on the small subset of risks that meaningfully increase attack surface. Over time, this reduces vulnerability backlog growth.
Faster Vulnerability Remediation
Automation significantly shortens remediation timelines.
Integrated workflows reduce the time spent manually analyzing vulnerabilities, coordinating tickets, and researching fixes. Teams can move from identification to resolution far more quickly.
Better Security and Engineering Alignment
Unified workflows improve collaboration between security and engineering teams.
Security analysts no longer deliver large lists of vulnerabilities without context. Instead, prioritized remediation guidance allows engineering teams to focus on specific fixes with clear risk reduction impact.
This approach aligns well with devsecops vulnerability management practices.
Improved Compliance and Reporting
Centralized vulnerability data simplifies compliance reporting.
Auditors and risk teams can easily access consistent information about vulnerability exposure, remediation timelines, and security posture management across the organization.
Unified Vulnerability Management in Cloud-Native Environments
Cloud-native environments introduce new challenges for vulnerability management.
Modern infrastructure is highly dynamic. Containers spin up and disappear within minutes. Cloud services continuously change configuration. Development teams deploy code multiple times per day.
These conditions dramatically expand the attack surface.
Traditional scanning approaches struggle to keep up with this level of change. Periodic scans may miss vulnerabilities introduced between scan cycles.
Unified vulnerability management is particularly valuable in these environments because it supports continuous monitoring across:
- multi-cloud infrastructure
- containerized workloads
- serverless platforms
- dynamic application environments
By integrating cloud vulnerability management and attack surface management data, unified platforms provide a constantly updated view of organizational risk.
This allows security teams to maintain both visibility and resolution capabilities even as infrastructure evolves rapidly.
How AI Is Transforming Vulnerability Management
Artificial intelligence is beginning to reshape how vulnerability management operates.
Historically, security analysts performed most vulnerability analysis manually. They reviewed scan results, evaluated risk context, and researched remediation steps.
AI-driven systems can now automate many of these tasks.
Examples include:
- AI-driven vulnerability prioritization based on exploitability analysis
- Automated attack path analysis against compensating controls
- Preemptive exposure management with insights
- Remediation simulations across all configuration flaws, patch and software issues.
These capabilities are particularly important as organizations move toward continuous threat exposure management models.
Instead of periodically reviewing vulnerability reports, security platforms can continuously analyze risk and recommend or implement corrective actions.
This shift allows security teams to move from reactive vulnerability management toward proactive exposure reduction.
How ZEST Enables Unified Vulnerability Management
Most organizations already have strong visibility tools in place. They run cloud scanners, application security testing tools, and infrastructure vulnerability scanners.
What they lack is an operational layer that turns those findings into resolved risks.
ZEST functions as that action layer within the security stack.
First, ZEST creates a unified data fabric that aggregates and normalizes vulnerability findings across cloud environments and security scanners, including on-premise, AWS, Azure, and GCP ecosystems. Instead of managing disconnected alerts, security teams work from a single operational view of risk.
Second, ZEST uses a Multi Agent AI system to simulate millions of possible resolution paths for each vulnerability. Rather than simply ranking risks, the platform determines the fastest and most effective way to eliminate exposure.
Third, ZEST supports both remediation and mitigation strategies. When patching is not immediately possible, the platform recommends cloud guardrails and configuration changes that block the exploit path and reduce exposure.
Finally, ZEST delivers Security as Code outputs that integrate directly into engineering workflows. The platform generates ready to implement fixes such as Terraform or CloudFormation templates that DevOps teams can review and approve quickly.
By combining these capabilities, ZEST enables organizations to move beyond passive vulnerability monitoring and toward active risk resolution.
Best Practices for Implementing Unified Vulnerability Management
Organizations adopting unified vulnerability management should focus on operational improvements rather than simply deploying another security platform.
Several best practices help ensure success.
Consolidate vulnerability tools where possible
Reducing the number of disconnected vulnerability scanning tools simplifies data correlation and operational workflows.
Prioritize risks based on exploitability
Severity alone is not a reliable indicator of real-world risk. Effective programs prioritize vulnerabilities based on exploit availability and attack paths.
Automate remediation workflows
Manual ticket management does not scale. Automated remediation pipelines dramatically improve response times.
Align security and engineering teams
Security teams must provide actionable remediation guidance rather than large vulnerability lists. Clear workflows reduce friction between teams.
Continuously monitor the attack surface
Organizations should combine vulnerability intelligence with attack surface management insights to maintain awareness of new exposures.
The Future of Vulnerability Management
The vulnerability management landscape is evolving rapidly.
Several trends are shaping the next generation of security operations:
- exposure management platforms that analyze attack paths across environments
- automated remediation capabilities that reduce manual effort
- AI driven security operations platforms
- dramatically shorter vulnerability response windows
As infrastructure becomes more dynamic, organizations will need systems capable of continuously identifying and resolving risks without heavy human intervention.
The future of cybersecurity will not revolve around managing vulnerability lists.
It will focus on automatically resolving exposure across the attack surface.
Frequently Asked Questions About Unified Vulnerability Management
What is unified vulnerability management?
Unified vulnerability management is a cybersecurity approach that consolidates vulnerability detection, prioritization, and remediation across multiple security tools into a single platform. It provides a unified view of risk and helps organizations resolve vulnerabilities faster by prioritizing exploitable attack paths.
How is unified vulnerability management different from vulnerability scanning?
Vulnerability scanning tools only detect security weaknesses in systems or applications. Unified vulnerability management platforms aggregate findings from many scanners and add prioritization, workflow automation, and remediation capabilities.
Why is vulnerability remediation so difficult?
Vulnerability remediation is difficult because security teams identify risks while engineering teams must implement fixes. Coordination delays, patch availability issues, and large vulnerability backlogs often slow the remediation process.
What tools support unified vulnerability management?
Unified vulnerability management typically integrates with cloud security platforms, application security scanners, infrastructure vulnerability scanners, and attack surface management tools.
However, integrations and correlations are not enough. UVM has shifted into Agentic Exposure Management and requires integrations with your cloud infrastructure, CI/CD and ITSM platforms.
The platform consolidates findings and coordinates remediation across these systems.
How does AI improve vulnerability management?
AI improves vulnerability management by automating vulnerability prioritization, analyzing attack paths, and generating remediation guidance. These capabilities help security teams resolve risks faster and reduce manual analysis work.
About The Author




.svg)