Continuous Threat Exposure Management (CTEM) is a five-stage cybersecurity framework, defined by Gartner in 2022, that helps organizations continuously discover, prioritize, validate, and remediate exposures across their entire attack surface based on real business risk rather than raw vulnerability counts. Unlike traditional vulnerability management, CTEM treats security as an ongoing, business-aligned program rather than a periodic scan-and-patch cycle.
By 2026, Gartner predicts that organizations prioritizing security investments based on a CTEM program will be three times less likely to suffer a breach. This guide explains what CTEM is, how the framework works, how it differs from vulnerability management and attack surface management, and how to operationalize a cloud-native CTEM program powered by agentic AI.
If you're running security for a cloud-heavy org in 2026, you already know the old vulnerability management playbook is toast. Ephemeral workloads spin up and down in minutes, attackers weaponize flaws in days (sometimes hours), and your attack surface now spans code, configs, containers, identities, and AI agents. Legacy VM, with its quarterly scans, CVSS-only triage, and ticket ping-pong, just can't keep up.
At Zest Security, we've helped dozens of teams move from reactive "find-and-fix" to proactive Continuous Threat Exposure Management (CTEM) supercharged by agentic AI. The result? Faster remediation, smarter patching, and breaches slashed by up to two-thirds.
For a deeper look at what CTEM really entails and how to operationalize it, see our CTEM practical guide
What Is Continuous Threat Exposure Management (CTEM)?
Continuous Threat Exposure Management (CTEM) is a structured, five-stage program (not a tool or product) that enables security teams to continuously identify, validate, and reduce the most critical exposures across their digital estate. Coined by Gartner in July 2022, CTEM shifts cybersecurity from periodic, audit-driven vulnerability scans to a continuous, threat-informed loop that aligns remediation with business priorities.
A CTEM program covers more than CVEs. It accounts for misconfigurations, identity and access risks, exposed secrets, attack paths, third-party SaaS exposures, and unmonitored shadow assets. In short, anything an attacker could exploit. The output is a prioritized, validated list of exposures that actually matter, paired with a closed-loop remediation workflow.
Quick definition for snippets: CTEM (Continuous Threat Exposure Management) is a cybersecurity framework that continuously discovers, prioritizes, validates, and remediates exposures across an organization's full attack surface, focusing on real business risk and exploitability rather than raw vulnerability counts.
Why CTEM Matters: The Market Shift Driving Adoption
Three structural shifts have made traditional vulnerability management obsolete and pushed CTEM from a Gartner concept to a board-level priority:
- The attack surface exploded. Modern organizations run workloads across multi-cloud, SaaS, hybrid infrastructure, AI agents, third-party APIs, and ephemeral compute. There is no longer a clean perimeter to scan.
- Attackers got faster. The median time-to-exploit dropped from 32 days in 2021 to roughly 5 days in 2025. Some vulnerabilities are exploited in "negative time," meaning before public disclosure.
- Vulnerability volume became unmanageable. Each cloud asset averages around 115 known vulnerabilities. No team can patch them all, so prioritization based on real risk (not CVSS scores) has become the only viable strategy.
The numbers from the field back this up:
- Over 100 zettabytes of data live in the cloud, with 88% of organizations operating in hybrid or multi-cloud environments.
- 80% of organizations are expected to experience a cloud data breach this year due to identity drift and unpatched exposures.
- 72% of 2025 breaches involved cloud data (IBM Cost of a Data Breach 2025).
- 23% of cloud incidents trace to misconfigurations alone, the #1 preventable cause.
- High and critical-severity MTTR still averages 55 to 74 days depending on asset type (Edgescan 2025 Vulnerability Statistics Report).
- 56% of vulnerabilities were weaponized within the first month of disclosure in 2025.
Gartner's prediction is the north star: organizations that adopt CTEM will be 3x less likely to suffer a significant breach by 2026.
How CTEM Works: The 5-Stage Gartner Framework
Gartner's CTEM framework defines five sequential, repeating stages. Each cycle should run continuously, typically every 1 to 3 months for the full loop, with discovery and prioritization running constantly underneath.
Stage 1: Scoping
Define which parts of the business the CTEM program will cover in this cycle. Scope is driven by business impact (crown-jewel applications, regulated data systems, customer-facing infrastructure, critical SaaS, identity providers), not by what's easiest to scan. Effective scoping aligns security and business stakeholders on what "exposure" actually means for the organization.
Stage 2: Discovery
Inventory all assets and their exposures within scope. This includes vulnerabilities, misconfigurations, exposed credentials, identity weaknesses, attack paths, and shadow assets. Cloud-native CTEM requires API-driven, continuous discovery (not periodic scans) to keep up with ephemeral resources.
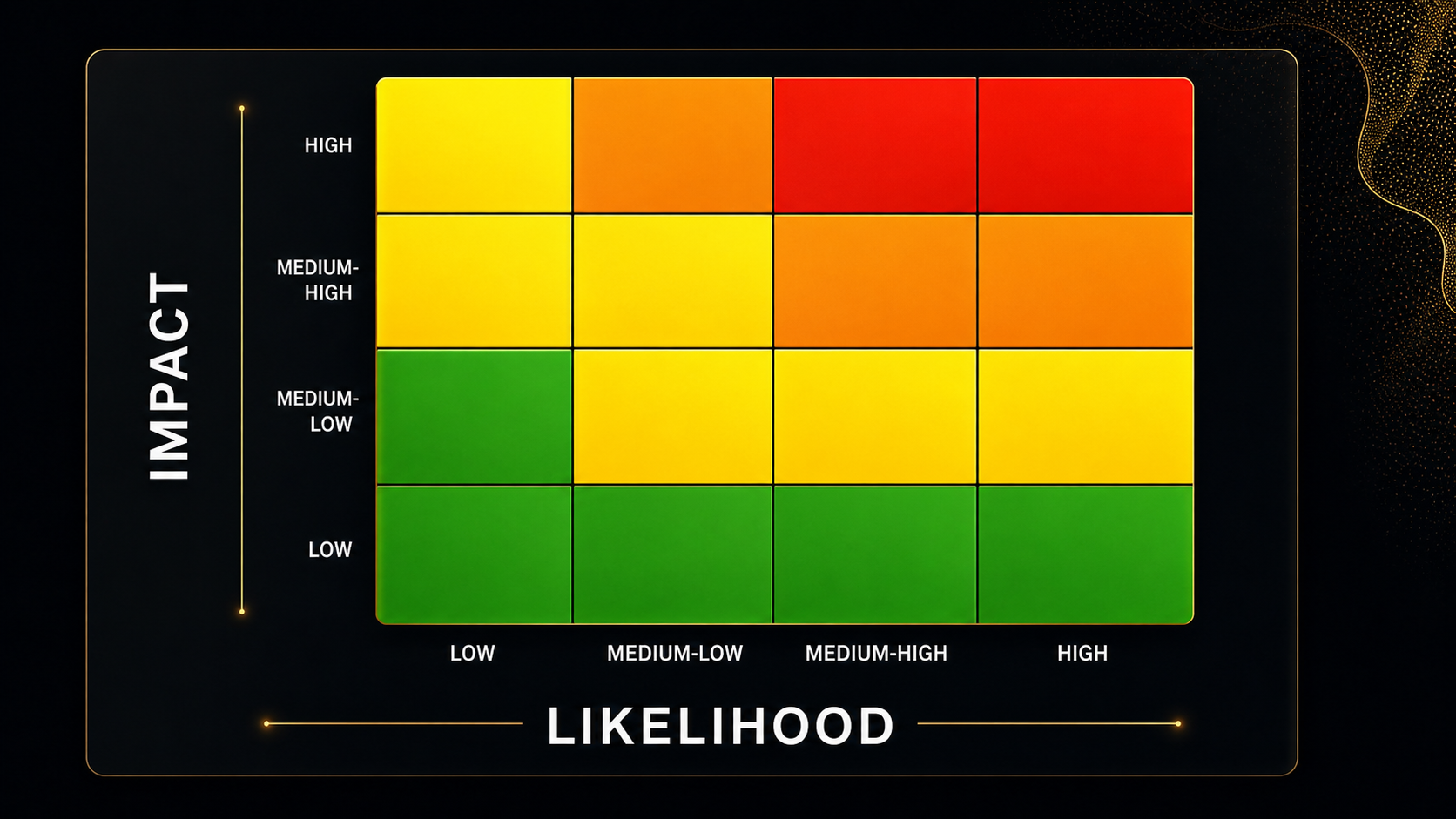
Stage 3: Prioritization
Rank exposures by real business risk, not raw severity. Prioritization factors include exploitability (CISA KEV, active exploitation in the wild), asset criticality, data sensitivity, network exposure, blast radius, and chaining potential. The goal is a short, ranked list of exposures that materially reduce risk if fixed.
Stage 4: Validation
Confirm that prioritized exposures are actually exploitable in your environment. Validation uses techniques like attack path analysis, breach and attack simulation (BAS), red teaming, and penetration testing. This stage filters out theoretical issues and confirms which exposures need urgent action.
Stage 5: Mobilization
Drive remediation through cross-functional workflows. Mobilization defines who fixes what, by when, and how. This includes SLAs, ticketing integrations, automated remediation, mitigations (such as compensating controls when patching isn't possible), and measurable outcomes. This stage is where most legacy vulnerability programs fail; CTEM treats mobilization as a first-class engineering problem.
The continuous loop: After mobilization, the cycle restarts. Scope expands, new assets appear, threat intel updates, and the program matures with each iteration.
CTEM vs Traditional Approaches: A Clear Comparison
CTEM is often confused with vulnerability management (VM), attack surface management (ASM), and risk-based vulnerability management (RBVM). Here's how they actually differ:
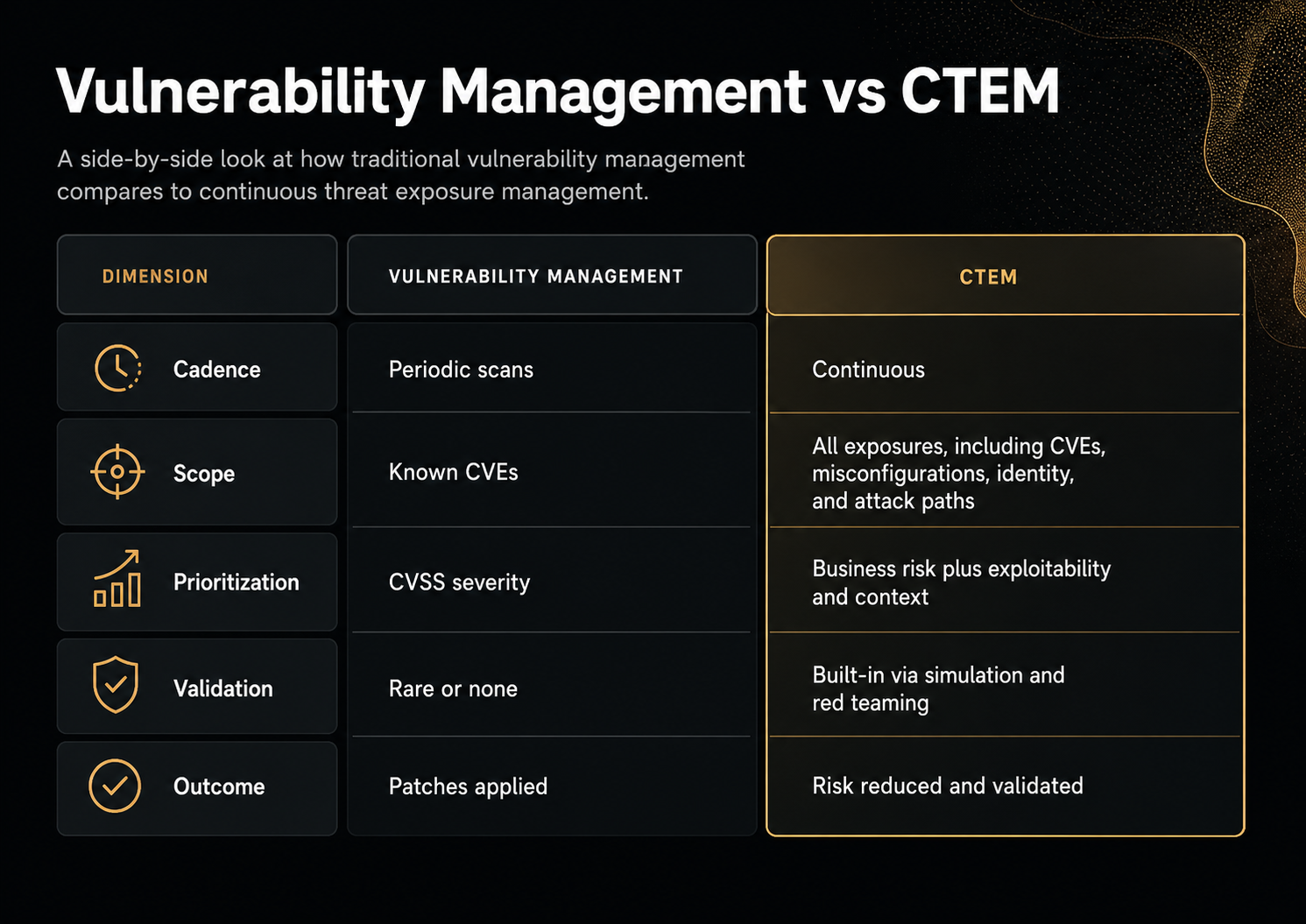
CTEM vs Vulnerability Management
Vulnerability management is a tactical, scan-driven process focused on identifying and patching known CVEs. It's typically periodic (monthly or quarterly), CVSS-based, and limited to assets the scanner can reach.
CTEM is a strategic, continuous program covering every type of exposure (CVEs, misconfigurations, identity risks, attack paths) prioritized by business impact and validated for real-world exploitability. CTEM uses VM as one input, not the whole program.
CTEM vs Attack Surface Management (ASM)
Attack surface management (ASM) discovers and monitors external-facing assets such as domains, IPs, exposed services, and leaked credentials. ASM is excellent at answering "what do attackers see?"
CTEM is broader. ASM is one input to the Discovery stage. CTEM also covers internal assets, identities, cloud configurations, and chained attack paths, and adds prioritization, validation, and mobilization on top of discovery.
In short: ASM tells you what's exposed. CTEM tells you what to fix first, proves it's exploitable, and drives the fix to closure.
CTEM vs Risk-Based Vulnerability Management (RBVM)
RBVM added risk context to traditional VM by factoring in exploitability and asset criticality. CTEM extends RBVM by including non-CVE exposures (misconfigurations, identity, attack paths), adding validation as a formal stage, and operationalizing remediation through mobilization. RBVM is essentially the prioritization engine inside a CTEM program.
Benefits of CTEM: Business and Technical Outcomes
A mature CTEM program delivers measurable improvements across both security and business metrics:
Technical benefits
- Faster remediation: MTTR for critical exposures drops 50 to 60% in mature programs.
- Reduced exposure window: Critical exposures get closed in days, not months.
- Lower noise: Risk-based prioritization shrinks the actionable backlog by 70 to 90%.
- Better coverage: Continuous discovery catches ephemeral cloud assets that periodic scans miss.
- Validated risk reduction: Each remediation is confirmed, not assumed.
Business benefits
- Up to 2/3 fewer breaches for CTEM adopters by 2026 (Gartner).
- Lower tool sprawl and operational cost through unified visibility.
- Audit-readiness by design, where continuous evidence replaces quarterly scrambles.
- Faster cloud innovation because security keeps pace with engineering velocity.
- Quantifiable risk reduction that can be reported to the board.
Cloud-Native CTEM: Why the Cloud Changes Everything
Cloud-native CTEM isn't traditional CTEM with a cloud module bolted on. The cloud's pace, scale, and architecture demand a fundamentally different approach.
What makes cloud-native CTEM different
- Ephemeral assets: Containers and serverless functions live for minutes. Discovery must be API-driven and continuous.
- Identity is the new perimeter: In cloud, an over-permissive IAM role often outweighs a CVE. CTEM must treat identity as a first-class exposure type.
- Configuration is code: Misconfigurations come from Terraform, CloudFormation, and Helm charts, so prevention belongs in CI/CD, not just runtime.
- Shared responsibility: The cloud provider secures the platform; you secure your configurations, code, and identities. CTEM scope must reflect this boundary.
- Attack paths span layers: A real cloud breach typically combines a vulnerable container, a misconfigured S3 bucket, and an over-privileged role. CTEM must correlate across layers, not silo them.
Key components of a cloud-native CTEM program
A modern program isn't another scanner. It's a continuous, context-aware, collaborative loop: discover, prioritize, remediate, validate, powered by agentic AI for autonomous patching where it makes sense.
1. Unified Exposure Management Across the Full Stack
Stop treating code flaws, cloud misconfigs, container CVEs, secrets, and identity risks as separate problems. A modern unified vulnerability management strategy brings them into one correlated view:
- App code and open-source dependencies (SAST/SCA)
- Cloud infrastructure misconfigurations (CSPM)
- Containers and hosts
- Secrets and overly permissive IAM
- Identity risks that amplify everything else
The benefit is complete visibility and combined context: "this container vuln plus public S3 bucket plus exposed workload equals critical exposure." Teams see one prioritized backlog per app or cloud project.
2. Risk-Based Prioritization
Ditch pure CVSS. Factor in:
- Asset criticality and business impact
- Real exploitability and threat intel (CISA KEV, active campaigns)
- Exposure (internet-facing? sensitive data?)
- Chaining potential
Modern platforms calculate a contextual risk score automatically. A "medium" on a crown-jewel production system jumps to urgent; a "critical" on an isolated test box gets deprioritized.
3. DevSecOps Workflows: Continuous Scanning and Automated Remediation
Embed security directly into CI/CD pipelines through a modern application security program
- Real-time discovery (new asset gets scanned in minutes)
- CI/CD gates that fail builds on critical exposures
- Auto-PRs to bump vulnerable libraries (Dependabot-style, but smarter)
- Agentic AI that detects a new critical vuln, finds every instance, assesses exposure, opens fix PRs or triggers immutable redeploys, then validates, all autonomously for routine cases
MTTR for many orgs drops 60%+ with this. Patching becomes part of normal velocity, not a fire drill.
For security leaders, our runtime visibility and intelligent remediation webinar explores how runtime insights feed into fast, contextual fixes.
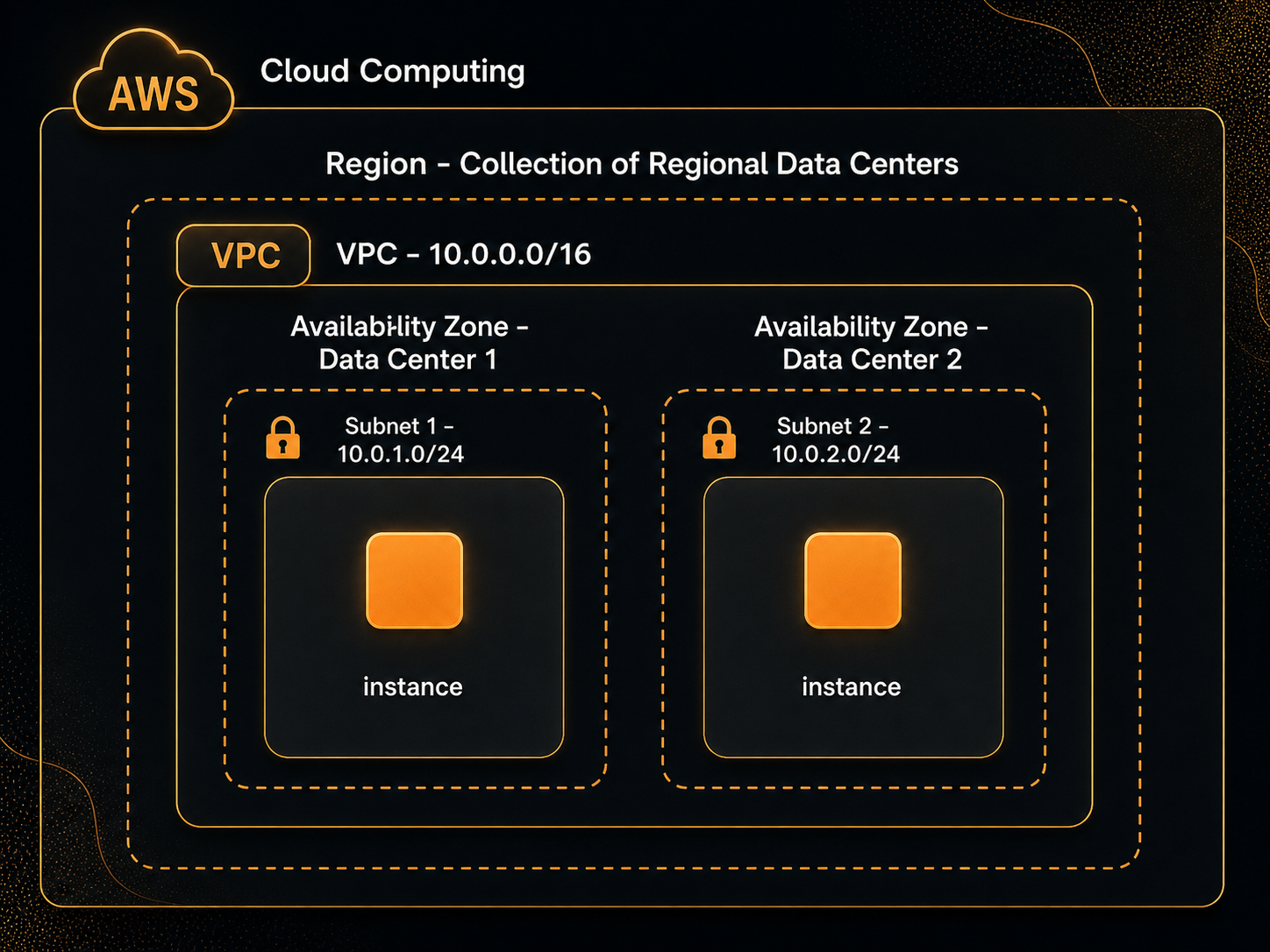
4. Cloud Network Segmentation: Contain the Blast Radius
Segmentation is your force multiplier. Use VPCs, security groups, NSGs, and micro-segmentation to isolate:
- Production from dev/test
- Sensitive data workloads
- East-west traffic between services
If a vuln is exploited, lateral movement stops cold. Integrate with your exposure platform so high-risk assets automatically get stricter policies (for example, "internet-facing plus known exploited vuln equals quarantine segment").
5. Enforceable Security Policies
Define clear, automated policies as part of a structured exposure mitigation program
- Critical exposures patched or remediated in 14 days
- No public S3 buckets without approval and encryption
- Least-privilege IAM enforced on every new role
- IaC scanning gates in Terraform/CloudFormation pipelines
Agentic AI plus CSPM can auto-enforce or escalate. With 31 to 56% of cloud challenges still tied to misconfigs, policies are non-negotiable for CTEM maturity.
6. Shared Responsibility Model Done Right
- Devs own code and dependency fixes
- Cloud/DevOps owns infra configs, base images, patching
- SecOps orchestrates, provides context, tracks risk posture
- FinOps helps quantify cost vs. risk (shutting idle resources means smaller attack surface plus lower bill)
- Business owners approve exceptions with eyes wide open
7. Agentic Exposure Management: AI That Doesn't Just Detect, It Fixes
This is where the AI era shines. Agentic AI goes beyond alerts:
- Predicts which exposures will actually get attacked
- Summarizes advisories in plain English
- Orchestrates multi-step remediation (find, assess, patch, verify, close)
- Handles 70 to 80% of routine work autonomously, escalating only the hard stuff to humans
At Zest, our agentic layer turns exposure data into resolved risk at machine speed.
8. Defense-in-Depth: From Build-Time to Runtime
Shift-left scanning, hardened IaC, runtime protection (CWPP, EDR, WAF), mitigations (temporary firewall rules, privilege reduction), and periodic pen tests. Even if one layer misses something, the others catch it.
9. Governance, Compliance, and Audit-Ready by Design
Policies with SLAs, formal exception/risk-acceptance workflows, full audit trails, and on-demand reports. Compliance becomes a byproduct, not a scramble. Maps cleanly to NIST, ISO 27001, PCI-DSS, HIPAA, and SOC 2.
How to Implement CTEM: A Practical Roadmap
Implementing CTEM is a maturity journey, not a one-time deployment. Most organizations move through four phases (Crawl, Walk, Run, Fly) over 6 to 24 months. The fastest movers compress this by adopting an agentic AI platform that automates discovery, prioritization, and remediation from day one.
Crawl (Months 0 to 3): Foundations
- Build a complete asset inventory across cloud, code, and identity.
- Enable basic continuous scanning (CSPM, SAST, SCA, container scanning).
- Fix the obvious criticals: known-exploited vulnerabilities (CISA KEV) on internet-facing assets.
- Define initial scope: what are the top 5 crown-jewel applications?
Walk (Months 3 to 6): Context and Process
- Add risk context: asset criticality, data sensitivity, exposure, threat intel.
- Define SLAs by risk tier (for example, critical = 14 days, high = 30 days).
- Integrate with ticketing (Jira, ServiceNow) and ChatOps (Slack, Teams).
- Establish ownership: which team fixes which exposure type?
Run (Months 6 to 12): Automation and Unification
- Deploy a unified exposure platform that correlates across layers.
- Add CI/CD security gates and auto-PRs for routine fixes.
- Implement validation through attack path analysis or BAS.
- Track and report MTTR, risk-weighted backlog, and SLA compliance.
Fly (Months 12+): Agentic CTEM
- Full agentic remediation for routine exposures.
- Continuous validation across all stages.
- Business-aligned risk decisions backed by quantified exposure data.
- Board-level reporting on risk reduction trends.
Metrics that matter at every stage:
- MTTR by risk tier: how fast you close what matters most
- Risk-weighted backlog: total open exposure expressed as risk, not count
- Coverage: percentage of assets continuously discovered (target: 100%)
- Known-exploited exposures open: goal of near zero
- SLA compliance rate: percentage of exposures fixed within policy
- Mean time to validate (MTTV): how fast you confirm exploitability
Challenges and Limitations of CTEM
CTEM is not a silver bullet. Honest assessment of the friction points:
Tool fragmentation. Most enterprises run 30+ security tools. Stitching them into a CTEM loop without a unifying platform produces dashboards, not outcomes.
Organizational change. CTEM requires SecOps, DevOps, AppSec, IAM, and business owners to operate as one system. This is a cultural shift, not just a tooling project.
Validation is hard at scale. Manually validating every exposure is impossible. Programs must rely on automated attack path analysis or breach simulation, which require investment.
Identity exposure is the hardest stage. Many CTEM programs underweight identity because it's harder to scan and correlate than infrastructure. In the cloud, this is a critical gap.
Skill scarcity. Mature CTEM requires practitioners who understand cloud, code, identity, and threat intel. Agentic AI helps close this gap by automating routine analysis and remediation.
The Future of CTEM: Where It's Heading
CTEM is evolving fast. Three trends will shape the next 24 months:
1. Agentic AI becomes the default execution layer. By 2027, most CTEM programs will run on autonomous agents that handle 70 to 80% of routine remediation, leaving humans to focus on novel risks and exception handling.
2. AI agents become a new exposure class. As organizations deploy AI agents inside production systems, CTEM scope must expand to cover prompt injection, agent identity sprawl, tool misuse, and shadow AI.
3. CTEM merges with security data fabrics. The next-generation CTEM platform won't just collect findings. It will normalize, correlate, and enrich security signals across every tool, becoming the single source of truth for cyber risk.
The organizations that win will be the ones that treat CTEM as an operating model, not a product category.
About The Author
.jpg)



.svg)