Security teams are buried. Vulnerability scanners flag thousands of issues. CSPM tools add thousands more. And the remediation backlog keeps growing while attackers move faster than ever.
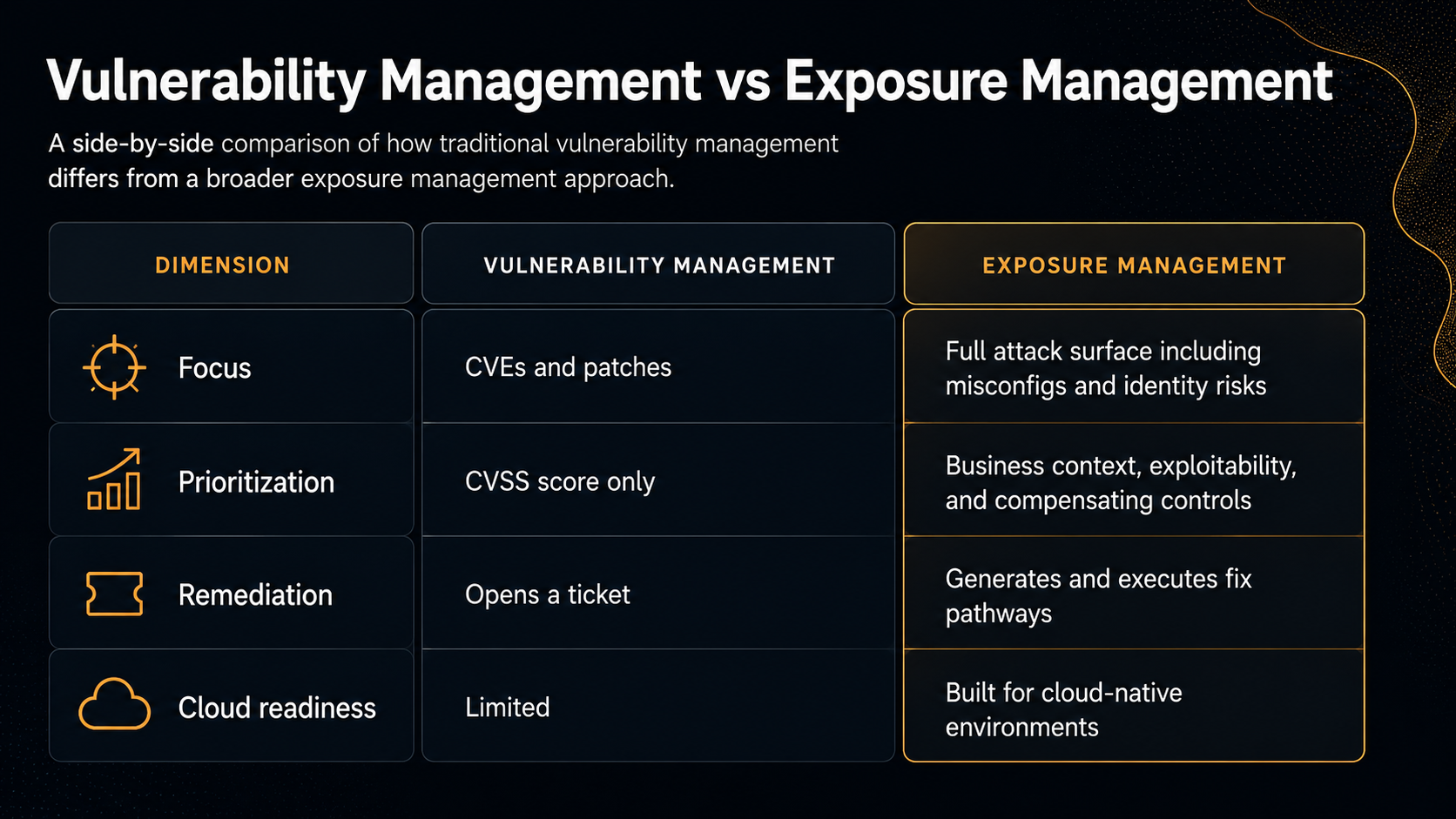
Traditional vulnerability management was never designed for this reality. It was built to scan, score, and report. Not to solve.
Exposure management fills that gap. And when powered by agentic AI, it becomes the most important shift in cloud security in a decade.
What Is Exposure Management?
Exposure management is a continuous, risk-based security discipline that identifies, prioritizes, and resolves vulnerabilities, misconfigurations, and weaknesses across an organization's attack surface before attackers can exploit them.
Unlike point-in-time scanning, exposure management is:
- Continuous, not periodic
- Context-aware, not just CVSS-score-driven
- Action-oriented, not just report-generating
- Remediation-focused, not just visibility-focused
It answers three questions every security team needs answered:
- Where are we exposed?
- What actually poses real risk in our specific environment?
- How do we fix it, or at least contain it?
Why Traditional Vulnerability Management Falls Short
Legacy VM tools were designed for on-premises infrastructure and quarterly patch cycles. Cloud environments have fundamentally outpaced what they can handle.
Core Components of an Exposure Management Program
A mature exposure management program consists of five interconnected capabilities:
1. Asset Discovery and Visibility
You cannot manage what you cannot see. A complete asset inventory across cloud environments, SaaS applications, identities, and endpoints is the foundation of exposure management.
This includes:
- Cloud workloads and containers
- Internet-facing assets and APIs
- IaC configurations and code repositories
- Third-party integrations and shadow IT
2. Exposure Identification
Not all exposures are CVEs. Modern exposure management accounts for:
- Software vulnerabilities (CVEs)
- Cloud misconfigurations
- Identity and access management (IAM) weaknesses
- Exposed secrets and credentials
- Network and API exposure
- Attack path risks
3. Risk-Based Prioritization
Raw vulnerability counts are meaningless without context. Effective prioritization weighs:
- Exploitability - Is there a known exploit? Is it being used in the wild?
- Business context - Does this asset process sensitive data? Is it internet-facing?
- Compensating controls - Does a WAF, VPC rule, or SCP already reduce the blast radius?
- Remediation effort - What does fixing this actually require?
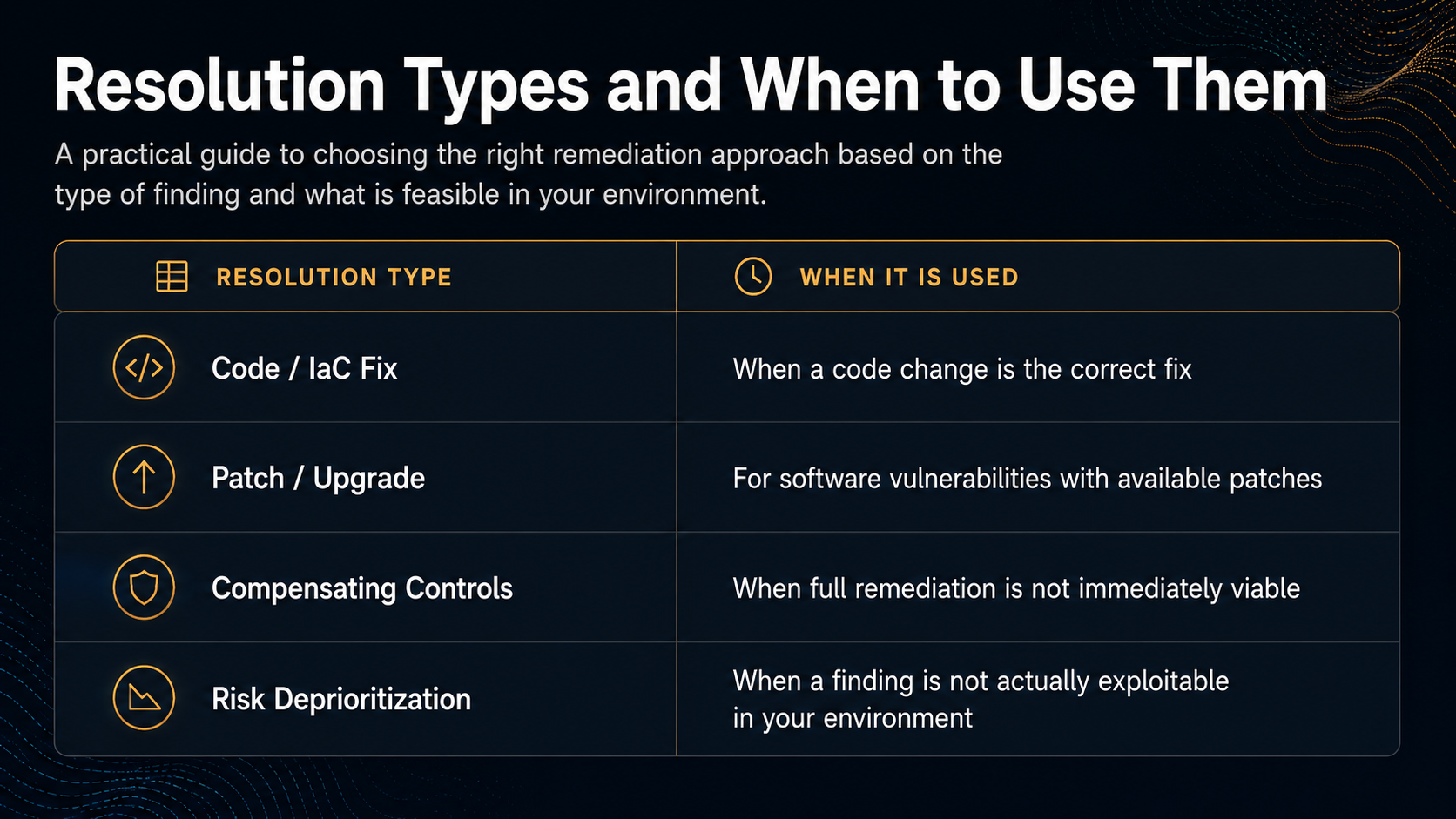
4. Remediation and Mitigation
This is where most programs fail. Exposure management must deliver more than a prioritized list - it must deliver a path to resolution:
- Code and IaC fixes
- Patch and upgrade pathways
- Compensating controls (WAF rules, SCPs, GuardDuty configurations)
- Risk acceptance documentation when no fix is available
5. Continuous Validation and Measurement
Exposure management is not a project, it's a program. Security teams need ongoing visibility into:
- Mean time to remediate (MTTR)
- Exposure age trends
- Remediation backlog velocity
- Risk reduction over time
The Numbers Behind the Crisis
- 131 vulnerabilities disclosed every day in 2025 (NVD)
- 56% of cloud risks cannot be immediately remediated (ZEST Security, Cloud Risk Exposure Impact Report)
- The median time to exploit a cloud vulnerability dropped to under 72 hours
- The average time to remediate a critical vulnerability still exceeds 60 days
- Organizations spend over $2 million annually on remediation toil (ZEST Security)
The math does not work. Attackers exploit in hours. Defenders remediate in months. The gap in between is where breaches happen.
The Biggest Exposure Management Challenges
Alert fatigue. Security teams are buried in overlapping findings from multiple tools. Most of it is noise that makes real risk invisible.
Remediation bottlenecks. Security finds the issue. Engineering owns the fix. The gap between those two teams is where remediation dies. Tickets sit unresolved for weeks.
The 56% problem. More than half of identified cloud risks cannot be immediately fixed. No patch available, legacy systems, or resource constraints. Without a mitigation strategy, these risks get accepted.
Cloud attack surface expansion. Cloud environments change constantly. New containers, APIs, and IaC deployments create new exposure every day. Yesterday's scan is already out of date.
What Is Agentic Exposure Management?
Agentic exposure management is what happens when AI does not just advise security teams, it acts on their behalf.
Traditional AI in security is advisory: "Here is what we found. Here is our recommendation." Agentic AI is operational: "Here is the fix. Here is the code. Here is the compensating control. Approve and deploy."
ZEST's platform deploys a network of specialized AI agents that work together to:
- Ingest and deduplicate findings from your existing security tools
- Contextualize each risk against your specific cloud environment
- Simulate every available remediation path and select the most effective one
- Generate actual Terraform code, IaC fixes, and configuration changes
- Apply compensating controls (WAF rules, SCPs, GuardDuty) when direct remediation is not immediately possible
- Route the right fix to the right team, with full context, automatically
How ZEST Security Approaches Exposure Management
ZEST Security is the leading agentic exposure management platform built for cloud environments. The platform shifts the focus from finding risks to actually resolving them.
ZEST integrates with the tools your team already uses: Wiz, Orca, Prisma Cloud, Qualys, Tenable, Rapid7, Jira, Terraform, and major cloud providers including AWS, Azure, and Google Cloud.
Key Benefits
For security teams: Cut through alert noise, prioritize what actually matters, and watch the remediation backlog shrink instead of grow.
For DevOps teams: Receive specific, reviewable code fixes with full context instead of vague ticket descriptions that require hours of additional research.
For CISOs: Report on measurable risk reduction, not just vulnerability counts. Demonstrate a proactive security posture to boards and leadership.
About The Author
.jpg)



.svg)