In 2025, Gartner® released an emerging technology report on preemptive security solutions. The report, titled Emerging Tech: Build Preemptive Security Solutions to Improve Threat Detection (Part 2), in which ZEST was named a sample vendor for preemptive exposure management, explores how preemptive security enables organizations to strengthen their defenses against emerging threats.
As AI-driven threats continue to compress attack timelines in 2026, this research is even more relevant today. Boards and executive leadership are no longer asking whether to adopt AI in security. They are asking how to do so without expanding organizational risk.
Why the Shift to Preemptive?
Attackers are increasingly leveraging AI to automate attack techniques, enabling them to gain initial access and execute critical attack stages at a faster speed than ever before. Attackers are innovating and operating at such a rapid pace that a reactive approach – especially when it comes to managing risk exposure – is no longer sufficient.
In 2026, threat actors are combining generative AI, automation frameworks, and cloud-native tooling to weaponize misconfigurations and exposed services within minutes of discovery. This acceleration has dramatically expanded the enterprise attack surface, particularly across SaaS, multi-cloud, and software supply chain ecosystems.
A preemptive approach is now critical – one that incorporates the latest advancements in AI to increase the speed and accuracy at which defenders can proactively prevent or disrupt attacks before they can launch or advance.
Preemptive cybersecurity is no longer a forward-looking concept. It is becoming a foundational requirement for organizations that must demonstrate measurable risk reduction to regulators, insurers, and boards.
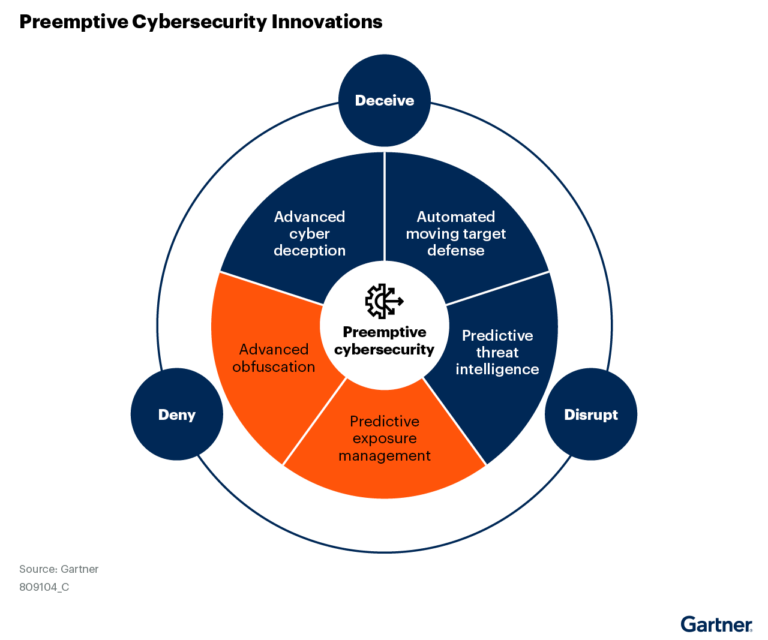
The concept of preemptive security extends beyond exposure management, applying across multiple areas including:
- Preemptive exposure management
- Advanced obfuscation
- Threat intelligence
- Advanced cyber deception
- Automated moving target defense
Preemptive Exposure Management Explained
As defined by Gartner®, preemptive exposure management “is not a separate technology category; it is a progressive approach to executing exposure management”.
While exposure management is inherently proactive, with the goal of reducing exposure by addressing vulnerabilities, misconfigurations, and other risks before attackers can exploit them, traditional approaches have fallen short, especially in complex cloud environments.
Today, the conversation has evolved beyond simply identifying vulnerabilities. Organizations are prioritizing continuous validation, remediation automation, and intelligent attack surface management to ensure that identified risks are actually resolved, not just reported.
Preemptive exposure management aims to address these critical gaps by streamlining risk management as an end-to-end process using innovations such as AI and intelligent simulation to enable faster and more precise remediation and mitigation actions.
This evolution aligns closely with broader Continuous Threat Exposure Management initiatives, which have gained enterprise-wide adoption since 2025.
A preemptive exposure management approach or solution enables security teams to:
- Prevent attackers from initiating attacks, for example exploiting open vulnerabilities, misconfigurations and other risks
- Disrupt ongoing attacks at various stages, for example reconnaissance, lateral movement, privilege escalation, and data encryption
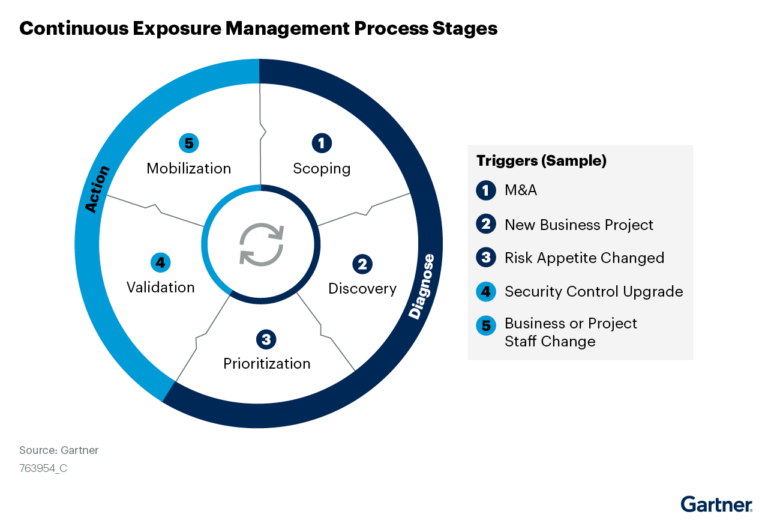
How Preemptive Exposure Management Aligns to Continuous Threat Exposure Management (CTEM)
As noted in the report, to truly move from a proactive to preemptive approach for exposure management, critical process stages of CTEM must be addressed, from discovery to mobilization.
- Discovery: Identification of risks including vulnerabilities, misconfigured assets, posture issues, etc.
- Prioritization: Prioritization of findings based on risk, exploitability, reachability, business criticality, availability of mitigating controls, impact on the risk backlog and remediation effort.
- Validation: Validation of threats, their impact, and remediation efficacy.
- Mobilization: Execution of precise remediation or mitigation actions.
Since the original publication of this report, regulatory pressure has intensified globally, with frameworks emphasizing continuous risk visibility, timely remediation, and executive accountability. This shift reinforces the need for organizations to operationalize exposure management rather than treat it as a periodic assessment exercise.
The Link Between Exposure Management and Threat Detection and Response
To enhance detection and response, integrating preemptive capabilities, including preemptive exposure management is key.
Modern security operations now depend on closed-loop systems where detection insights continuously inform exposure prioritization, and remediation outcomes refine detection logic. Without this feedback loop, security teams risk perpetuating alert fatigue and unresolved exposure backlog.
A preemptive exposure management approach not only bridges the gap between identifying risk findings and applying solutions – reducing the time and complexity of remediation and mitigation efforts. It also ensures that the solutions you implement today also prevent future and recurring risks. For example, a preemptive approach enables organizations to implement a feedback loop to continuously refine and enhance detection mechanisms.
How ZEST Delivers Preemptive Exposure Management
ZEST streamlines end-to-end remediation operations, leveraging Agentic AI to drastically reduce the complexity and time it takes to resolve cloud security, AppSec issues and other risks.
As organizations mature their AI governance strategies in 2026, security leaders are seeking AI systems that augment human teams rather than replace them. ZEST’s approach extends security teams with specialized AI agents designed for precision remediation and intelligent simulation, supporting scalable preemptive self-defense without increasing operational burden.
As an AI agnostic solution, the platform employs various LLMs and AI Agents that excel in specific remediation tasks, extending and enhancing security teams. The platform offers a unified view of prioritized findings including vulnerabilities, AppSec issues, misconfigurations, and software supply chain risks, and delivers fully guided remediation and mitigation.
Core Capabilities:
- AI-generated resolutions: AI agents examine infinite options for resolution, mapping open findings to the best possible solution based on available fixes, remediations, and mitigations.
- Intelligent simulation: Simulates the implementation of patches, package updates, IaC and code fixes to determine which resolution paths resolve the most findings at once.
- Exposure validation: Validates risk exposure and that remediation and mitigation actions were effective to close the remediation loop.
- Seamless integration: Integration with the security stack including CNAPP, CWPP, CSPM, AppSec solutions, vulnerability management platforms, DevOps systems, and ticketing and communication and ticketing systems.
The Future of Preemptive Security
The next phase of preemptive cybersecurity will be defined by automation maturity, real-time attack surface validation, and board-level risk quantification. Organizations that successfully transition from reactive detection to continuous exposure elimination will be better positioned to withstand AI-enabled adversaries.
The question is no longer whether to adopt a preemptive model, but how quickly organizations can operationalize it at scale.
Ready to see ZEST in action?
To see how ZEST proactively identifies and resolves security risks before attackers can exploit them, schedule a demo of our agentic exposure management platform and explore our unique approach to preemptive exposure management.
About the Author
.jpg)

.svg)